AgileAssets support using SAML protocol to conduct Single Sign-On (SSO). This page shows how to setup SAML with Azure Active Directory as an example Identity Provider (IdP). For other Idps, the setup is similar.
|
Click to jump to a topic:
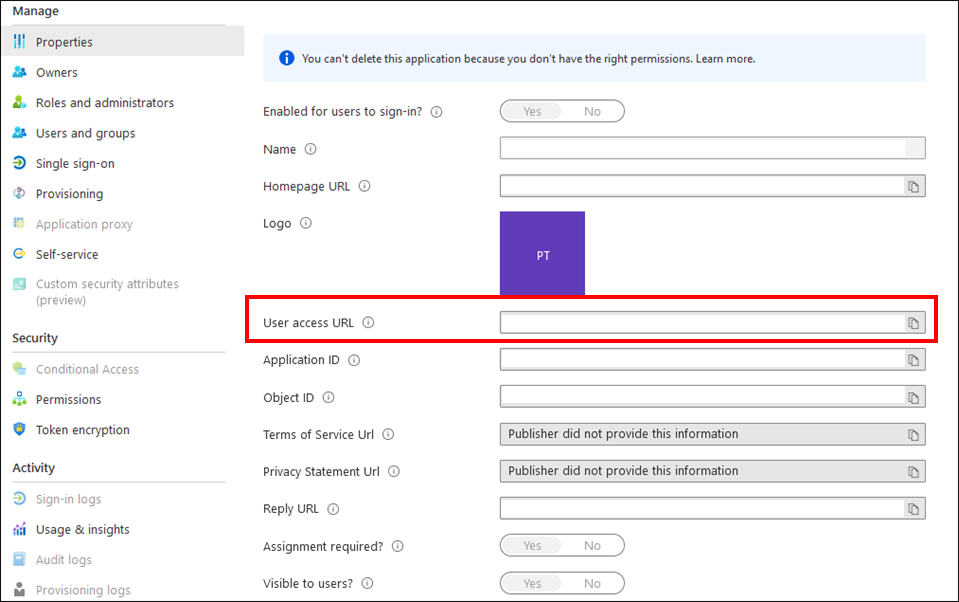
In the SSO page, ask client to enter these values for these fields:
Field | Value | Example |
|---|---|---|
| Identifier (Entity ID) | [Application Base URL] | https://quappv21.agileassets.com/ams-web |
| Reply URL (Assertion Consumer Service URL) | [Application Base URL]/alias/sp | https://quappv21.agileassets.com/ams-web/alias/sp |
Sign on URL | Leave empty | |
Relay State | Leave empty | |
Logout Url | Leave empty | |
| All other fields | Leave empty (or default value) |
Make the following changes in AMS's web.xml file under Tomcat application folder.
<filter> <filter-name>SamlFilter</filter-name> <filter-class>com.agileassetsinc.core.SsoSAMLFilter</filter-class> <init-param> <param-name>SIGNATURE_STRATEGY</param-name> <param-value>ASSERTION_SIGNATURE</param-value> </init-param> </filter> <filter-mapping> <filter-name>SamlFilter</filter-name> <url-pattern>/alias/sp</url-pattern> </filter-mapping |
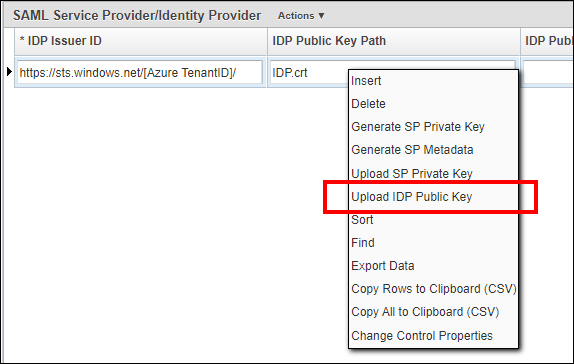
Insert a new row in the System > Setup > SAML Security screen, complete the following values and Save.
| Attribute | Value | Example |
|---|---|---|
| IDP Issuer ID | Use the entityID field value retrieved from FederationMetadata.xml | https://sts.windows.net/[Azure TenantID]/ |
| IDP Public Key Path | File name of the Certificate (Base64) file | IDP.cer |
| IDP Public Key Alias | Can be anything, e.g. "Microsoft Azure Federated SSO Certificate" | Microsoft Azure Federated SSO Certificate |
| SP Entity ID | Can be anything. e.g. user system name and environment | AMS-DEV |
| Allowed Skew Time (min) | The column "Allowed Skew Time (min)" enables some difference between the clocks. It's recommended that "Allowed Skew Time (min)" value has to be set between 1 and 3 (in minutes). | 3 |
| User ID mapping | NameID | NameID |
| Error Resource | If the authentication is rejected in AgileAssets (e.g., No corresponding AD_USER_ID or invalid SAML assertion) the URL where the request will be redirected. By default, it will go on the AgileAssets login page. | Blank |
| Issuer Assertion | Ensure checks are performed. | Checked |
Place the Certificate (Base64) file from Azure under [Tomcat Installation Folder]/webapps/[Application Name]/Certificates/ folder.
OR
Right click the record and select Upload IDP Public Key option. Select the Certificate (Base64) file from Azure and upload it.
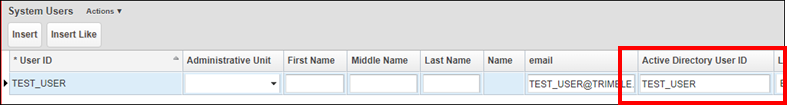
On the System > Security > User Level > User Names and Access window, add each user's Active Directory user name is added to the Active Directory User ID field. It may be the user's Azure User ID or email - depending on client's Azure configuration. If one does not work, try the other.